In its simplest form, a virtual private network or VPN is an encrypted private network connection (sometimes referred to as a "tunnel") between two machines or endpoints. One endpoint is the client machine, for example, a laptop or smartphone. The other endpoint is the VPN-targeted server you connect to before traffic goes off to the public Internet. The required VPN software consists of the software on your particular device, the VPN client software, and the VPN server software. These two pieces of software work together to provide the encrypted tunnel and can be obtained from a private for-profit firm or by using open-source software (OSS) like WireGuard that you configure and manage, typically at low to no cost. When the client machine authenticates and connects to the VPN server, the client appears to be coming from that server using its public IP address. For example, you connect to a EC2 instance on AWS that acts as the VPN server. When you open a browser and type What's my IP, the AWS server's public IP address is displayed instead of your home routers that your ISP hands out to you.
Some benefits of VPNs and why you would want to use one are bulleted below:
Privacy increases with VPN use as ISP logging and tracking of online activities diminish with encrypted traffic and traffic redirection through a private tunnel
A VPN is a must for travelers who need secure communications, often with limited safe choices for Internet connections
A VPN is essential to support remote workers when connecting to their place of business to access resources and is protective of data in transit
A VPN used for private citizens to connect back to their LAN for remote access to files and folders, IP camera footage, and servers provides suitable security
In many cases, you can get around local content restrictions and avoid oppressive government censorship and company Geo-restrictions regarding access to website content
With your actual IP hidden; advertisers have a difficult time tracking online activity used for pushing selected ads
With your traffic encrypted and IP hidden, security on public WIFI dramatically increases with the prevention of IP spoofing MitM attacks and evading session hijacking
A VPN used for site-to-site communications between offices or large departments typically can be set up on the gateway firewall for secure business communication
Your home router's public IP is replaced with the VPN server's public IP address, improving user privacy concerning Internet Service Provider snooping. While VPNs are primarily anonymous and limit the location and browsing history data collection, the VPN provider or cloud-hosted server is subject to some oversight and may store traffic logs or IPs. Generally, VPN protocols provide security, while privacy is dependent on the VPN service policy or implementation choices
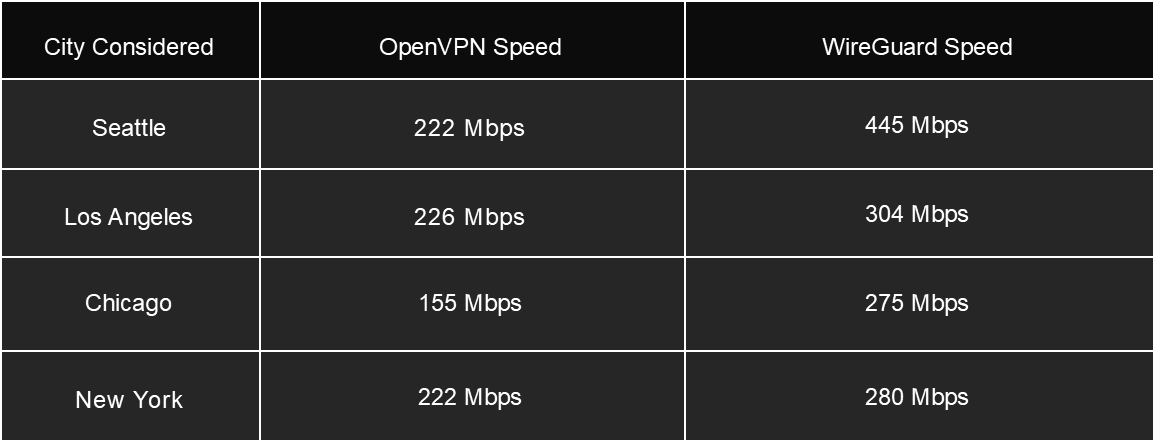
So, what is WireGuard? From their website, WireGuard is a secure VPN protocol (client and server), and it is much faster and leaner than OpenVPN or IPsec and much more straightforward to set up while being just as secure. Table 1 shows that when comparing the performance in Mbps of, say, OpenVPN to WireGuard, the delta is in WireGuard's favor.
Table 1
OpenVPN vs. WireGuard
WireGuard kernel components are released under the GPLv2 license and run within the Linux kernel as opposed to the OS user space. Furthermore, as noted, with fewer lines of code compared to behemoths like Swan/IPsec or OpenVPN/OpenSSL (hundreds of thousands vs. 4000), WireGuard is meant to be reviewed and audited by a single security team member with its significantly smaller attack surface. WireGuard features relating to agility and support, and cryptographic algorithms highlighted below consolidate the main features.
Agility and Support
WireGuard offers client apps for every major platform
WireGuard forms the base code for many paid-for VPNs in the market today
WireGuard connects and reconnects fast, even when you're roaming across networks. It stays connected in situations where other VPN protocols would hesitate.
WireGuard runs one set of ciphers and protocols, which leads to less complexity with far less code and a smaller attack surface, and immunity to downgrade attacks
WireGuard uses state-of-the-art cryptography and is actively under review by cryptographers.
WireGuard is easy to install, and you can download ready-to-go client apps for desktops and mobile devices from the platform app store
Cryptographic Algorithms
WireGuard uses modern, well-vetted cryptography with the following protocols and primitives.
ChaCha20 for symmetric encryption, authenticated with Poly1305, using RFC7539's AEAD construction
Curve25519 for ECDH
BLAKE2s for hashing and keyed hashing, described in RFC7693
SipHash24 for hashtable keys
HKDF for key derivation, as described in RFC5869
UDP as the transport layer protocol for much less overhead
Perfect Forward Secrecy (PFS) to protect user data supported
Finally, WireGuard uses public key encryption for identification and encryption, with secure key generation and management handled in the background, with an option to use a pre-shared key for an additional layer of security. Install information for WireGuard can be found here at https://www.wireguard.com/install/.
With part 1 (P1) of this three-part series, we will use the WireGuard VPN server and the WireGuard client to implement an essential VPN that is fast and secure and used by people who like to manage their VPN server and keys. Additionally, an Ubuntu EC2 instance on AWS will be our VPN server on which the WireGuard VPN service is installed and configured. With a small use case (1-5 clients), the chosen AWS AMI sits right above the free tier; however, for testing, you can use the free level if you like.
With the WireGuard client software on your mobile phone, tablet, or laptop, you connect to the AWS EC2 instance (WireGuard VPN server) and go out to the Internet to access resources using the AWS EC2s public IP. Remember, while using the VPN, your endpoint device assumes the EC2 public IP, so please be lawful in its use, as AWS does monitor what goes on within its platform. See PD004 for the implementation, and have fun building your VPN that you control😊
See You There!